What did you do on your computer is a physical? The password is now becoming obsolete, a real key will be more than a clever gimmick. In fact, right now on your PC may be the safest option to unlock require a physical element, and if you have a spare USB thumb drive lying around, you can set up a key in just a few minutes.
It would be better if the USB key password entries (eg, website) to replace all of the forms, but for now they are only able to handle locking and unlocking the PC. Perhaps we in the near future will see the progress.
USB Unlock Keys: The Good And The Bad
Depending on the security of the password alone is a big mistake that can cause problems for you down the road. Even if you create strong passwords and good safety habits, practices, one flaw remains: Once discovered, a password is useless. In that sense, a physical key is difficult to compromise, and it is difficult to steal than the elusive figure.
Another obvious benefit to himself, password memory to relieve the burden, although this is an issue less than a secure password manager is used. Additional benefits of using software to create a USB key, depending on the existing.

One, if you suffer from headaches if anything you’ll ever lose or damage the USB key; How to reset a password recovery more than a headache. The other drawback is the key to permanently replace the USB port and you want to grant access to someone else, you have to physically hand their core.
Predator [Windows]
Predator is a USB drive into an access control device for turning one of the most popular tools. It’s no limitations or missing features for personal and non-commercial use completely free with, but professional and commercial environment, it is $ 30 US dollars per computer. Not a bad price at all, considering what it does.
As long as the USB drive is plugged in, the computer is used as the access is completely remain intact allowed.USB drive. No files will be deleted or changed in any way.
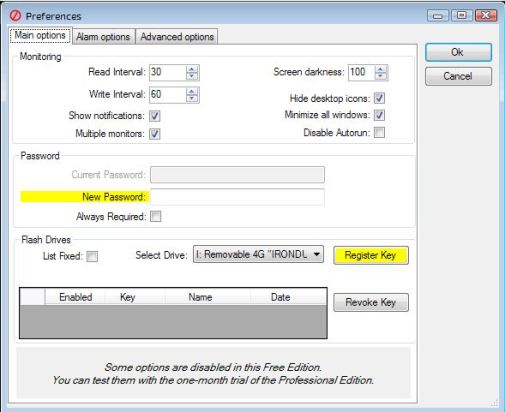
Advanced features include:
One USB drive can be used to lock/unlock multiple computers.
Multiple USB drives can be assigned to various users.
Built-in scheduler that can limit computer access to certain times of day.
Schedules can be determined on a per-user basis.
In case of a lost or broken USB key, per-user passwords can be entered instead.
The USB drive security codes are regularly changed, limiting the effectiveness of copied USB drives.
If you are a quick and easy solution that is just as long as you’re running Windows, and has worked as a spare USB port All in all you want, your best bet hunters. It is on this list with its built-in scheduler and per user customization of the most powerful and flexible program. You will not find those features of its competitors.
To set up your first USB key with Predator:
Install Predator.
Run Predator.
Insert your USB drive when prompted.
Enter a password for this user.
Select the drive that represents the USB device.
Click the Register Key button.
Done!
Rohos Logon Key [Windows & Mac]
Rohos Logon Key is a multi-platform access control program that’s available to create USB keys on Windows and Mac. There is an unlimited free version with several key features missing (no pun intended), though it’s only available for Windows. If you want full security and protection or if you’re using a Mac, then you’ll need to pay the full $32 USD.
Rohos works by storing your logon information and automatically inputting your credentials when the USB is plugged in. Alternate logon methods exist for Android and iOS, allowing you to unlock access to your Windows or Mac computer through your smartphone.

Features include:
Secure two-factor authentication by means of USB key + PIN code.
Emergency logon system that grants you access in case of a lost or broken USB or a forgotten PIN code.
Passwords stored on USB key devices are encrypted with AES-256 and protected against unauthorized duplicates.
As far as ease of setup is concerned, I have seen Rohos be a little easier and more straightforward than the hunters. However, that’s probably because Rohos is a simple program that is fundamentally different. This type of identity card replaces a literal: unlock the screen, you can plug it in to unlock.
This, of course, it is less secure than the hunter, so I will only use Rohos especially if you keep hunter-plug functionality of the USB-to-access login credentials as needed rather than effectiveness.
To set up your first key with Rohos Logon Key:
Install Rohos Logon Key.
Run Rohos Logon Key.
Insert your USB drive.
Type in your Windows password.
Click the Setup USB Key button.
Done!
USB Lock [Mac]
USB Lock is a Mac application for Windows that is similar to hunters: What does it grant access to a computer, as long as the USB key is plugged into the USB drive active Unplugging the USB drive immediately lock the computer with a USB key lock .. any way to create a file on your drive will not affect.
It is in the locker screen text input passwords and other patterns based on grid-swipe in the midst of a unique solution. The only downside is that there is a free version available, but for a price as low as $ 3 dollars, it’s definitely worth the cost.
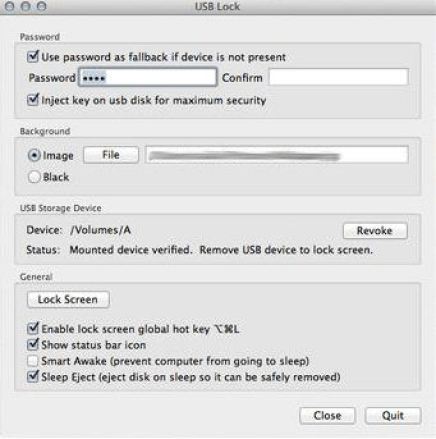
Features include:
Optional password requirement on top of the USB key requirement.
Does not sleep or close applications when entering locked mode.
Idle timer that locks the system during inactivity. (Coming soon)
When all is said and done, the USB-lock light is essentially hunters. USB key is plugged into the computer in order to enjoyable – – it’s the same core, but it serves the purpose of extra bells and whistles that awesome predators (eg, scheduling and customization per user) does not have to.
However, seeing how hunters are only for Windows, USB lock the earliest there is no alternative for Mac users. Only use it if you can spare a full USB port. You can not, then you could be better, instead of using Rohos.
To set up your first key with USB Lock:
Install USB Lock.
Run USB Lock.
Insert your USB drive when prompted.
Optionally enter a password if desired.
Done!
Have you turned your spare USB drives into physical keys? Give it a try with one of these tools and let us know how it works out for you in the comments below. It will be more effective than a single password and it may even end up being more convenient.